Technology
wa69utp: Meaning, Uses, and Why People Are Searching for It
The keyword wa69utp has recently started appearing across search engines, forums, and niche online discussions, leaving many people curious about what it actually means. Unlike common terms with a clear definition, wa69utp does not immediately point to a known concept, brand, or public figure. This makes it an interesting case of a modern digital keyword that may carry different meanings depending on the context in which it is used.
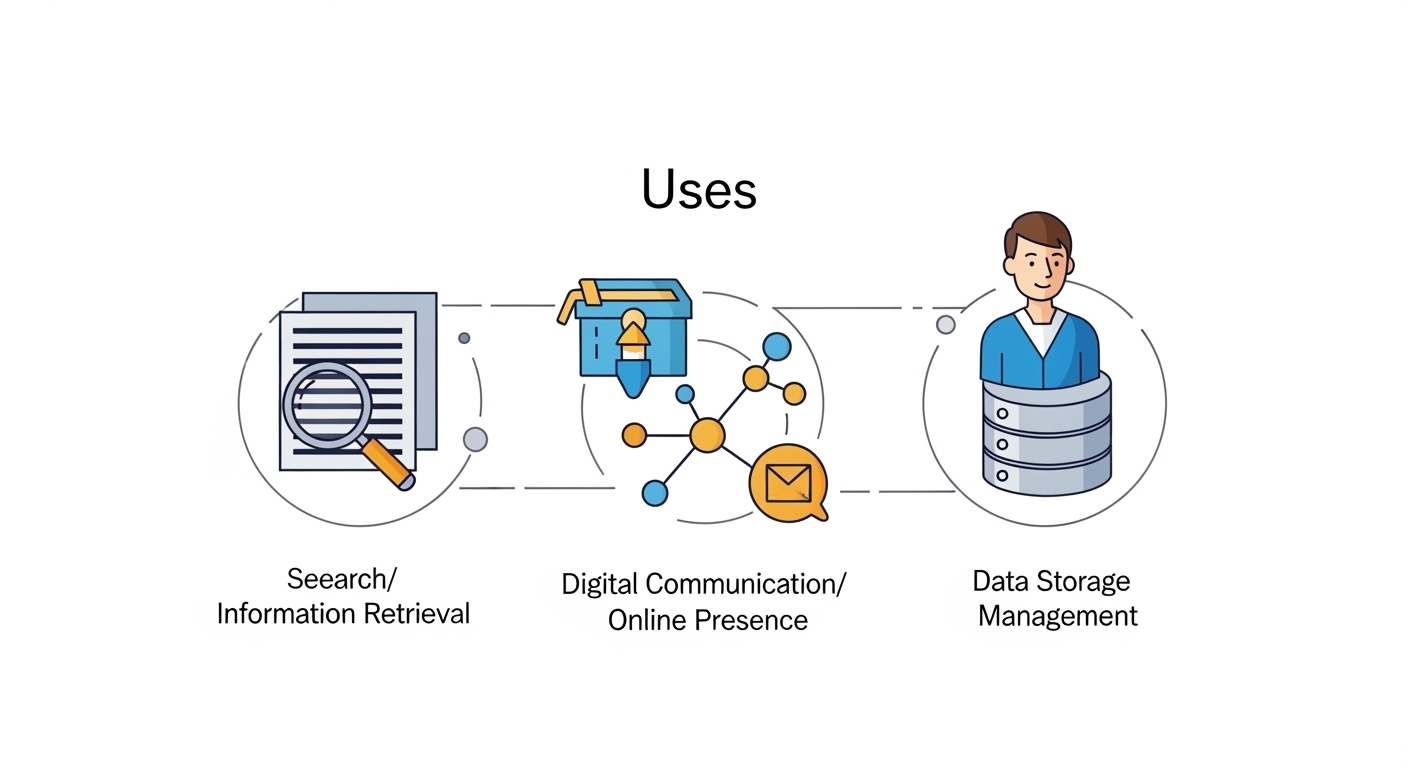
In today’s fast-moving internet culture, unique keywords like wa69utp often emerge from coded systems, usernames, private networks, or temporary digital identifiers. Some people encounter wa69utp while browsing websites, downloading files, or exploring online communities, while others see it as part of URLs, app data, or login references. Understanding such a keyword requires looking at its possible interpretations and the environments where it might appear.
This article explores wa69utp in detail, including its possible origins, how it is used online, why it is trending, and what users should keep in mind when encountering it. By the end, you will have a clearer idea of what wa69utp might represent and how to approach it safely and intelligently.
Understanding the Nature of wa69utp
At first glance, wa69utp appears to be a random combination of letters and numbers. However, such combinations are often not entirely random in the digital world. They can serve as identifiers, codes, or placeholders used in various systems. Many websites and applications rely on strings like wa69utp to label user sessions, track data, or generate unique references.
The structure of wa69utp suggests it could be an automatically generated string. Developers frequently use algorithms to create these types of codes for security or organization purposes. These identifiers help distinguish between different users, files, or actions without relying on easily guessable names.
In some cases, keywords like wa69utp gain attention because they appear repeatedly in a specific context. For example, users might notice the same code appearing in download links, redirect pages, or hidden sections of websites. This repetition can spark curiosity and lead to increased search activity, even if the keyword itself does not have a widely recognized meaning.
Possible Origins of wa69utp
The origin of wa69utp is not officially documented, which opens the door to several plausible explanations. One possibility is that it originated as a system-generated code within a web application or platform. Many online services use such identifiers to manage internal processes, and sometimes these codes become visible to users.
Another possibility is that wa69utp is part of a naming convention used in a specific community or niche. Online groups often create unique tags or codes to represent content, users, or shared resources. Over time, these tags can spread beyond their original environment and attract broader attention.
There is also a chance that wa69utp is linked to temporary or experimental content. Developers and testers often use random strings when building or testing new features. If such content becomes publicly accessible, users may encounter the code and begin searching for its meaning.
Common Places Where wa69utp Appears
People who search for wa69utp often report seeing it in various online locations. One common place is within URLs. It may appear as part of a link, especially in cases where websites use encoded parameters to track user activity or direct traffic.
Another place where wa69utp might show up is in file names or download links. Some platforms assign unique identifiers to files to prevent duplication or confusion. These identifiers can look similar to wa69utp and may remain visible even after the file is shared publicly.
Additionally, wa69utp could appear in user-generated content such as usernames, forum posts, or comments. Some individuals intentionally create unique names using combinations of letters and numbers, either for privacy or personal branding. If such a name gains visibility, it can quickly become a searchable keyword.
Is wa69utp a Code, Username, or Hidden Reference?
One of the most common questions about wa69utp is whether it represents a code, a username, or something else entirely. The answer depends largely on the context in which it is found. In many cases, it is likely a code generated by a system rather than a meaningful word.
When used as a code, wa69utp may function as a unique identifier. This could include session IDs, tracking codes, or database references. These codes are essential for the smooth operation of digital platforms, even though users may not always understand their purpose.
On the other hand, wa69utp could also be a username or alias. Some users prefer to remain anonymous online and choose random combinations of characters as their identifiers. If such a username becomes associated with specific content, it may attract attention and searches.
There is also the possibility that wa69utp is a hidden reference or shorthand used within a particular group. In this case, its meaning would only be clear to those familiar with that group’s context, making it appear mysterious to outsiders.
Why wa69utp Is Gaining Attention
The growing interest in wa69utp can be attributed to several factors. One major reason is curiosity. When people encounter an unfamiliar term, especially one that appears repeatedly, they naturally want to understand what it means.
Another factor is the way search engines and algorithms work. As more people search for wa69utp, it becomes more visible in search suggestions and trending topics. This creates a cycle where increased visibility leads to more searches, even if the original meaning remains unclear.
Social media and online forums also play a role in spreading such keywords. If users begin discussing wa69utp or sharing links that include it, the keyword can quickly gain traction. In some cases, it may even become a temporary trend within certain communities.
Potential Risks and Considerations
While wa69utp itself may not be harmful, it is important to approach unknown keywords with caution. If the term appears in links or downloads, users should verify the source before clicking or accessing any content. Not all links are safe, and some may lead to unwanted or harmful material.
Another consideration is privacy. If wa69utp is part of a tracking system, it may be used to monitor user activity. While this is common in many online services, users should be aware of how their data is being used and take steps to protect their privacy when necessary.
It is also wise to avoid making assumptions about the meaning of wa69utp without reliable information. Jumping to conclusions can lead to misunderstandings or unnecessary concern. Instead, users should rely on credible sources and context to interpret the keyword.
How to Interpret Keywords Like wa69utp
Understanding a keyword like wa69utp requires a combination of observation and critical thinking. The first step is to look at where the keyword appears. Context is crucial in determining whether it is a code, a name, or something else.
Next, consider the structure of the keyword. Random combinations of letters and numbers often indicate automated generation, while more structured names may suggest intentional creation. This can provide clues about the keyword’s purpose.
Finally, it is helpful to look for patterns. If wa69utp appears in multiple places with similar characteristics, it is likely serving a consistent function. Recognizing these patterns can make it easier to understand how the keyword is being used.
The Role of Random Keywords in the Digital World
Keywords like wa69utp are a natural part of the digital landscape. As technology continues to evolve, the use of automated systems and unique identifiers becomes increasingly common. These identifiers help manage large amounts of data and ensure that systems run efficiently.
At the same time, the visibility of such keywords can create confusion for users. When internal codes become publicly visible, they may appear mysterious or significant, even if they are simply part of a routine process.
Despite this, random keywords also highlight the complexity and sophistication of modern digital systems. They serve as a reminder of the many layers that operate behind the scenes, often without users even realizing it.
Could wa69utp Become Something Bigger?
It is possible for a keyword like wa69utp to evolve beyond its original purpose. In some cases, random strings gain meaning over time as they are adopted by communities or associated with specific content. This can transform a simple code into a recognizable term.
However, not all keywords follow this path. Many remain obscure and fade away as quickly as they appear. Whether wa69utp becomes more widely recognized depends on how it is used and whether it continues to attract attention.
For now, wa69utp remains an example of how digital trends can emerge from unexpected sources. Its future will likely be shaped by user interest and the contexts in which it appears.
Conclusion: What wa69utp Really Means
In conclusion, wa69utp is best understood as a flexible and context-dependent keyword rather than a fixed concept. It may function as a system-generated code, a username, or a reference used within a specific environment. Its meaning is not universal, which is why it has sparked curiosity among users.
The rise of wa69utp highlights how modern internet culture can turn even the most obscure terms into searchable topics. By approaching such keywords with curiosity and caution, users can better understand their purpose and avoid potential risks.
Ultimately, wa69utp serves as a reminder of the ever-changing nature of the digital world. New terms and identifiers will continue to emerge, each with its own story and significance. Staying informed and aware is the best way to navigate this dynamic landscape.
Technology
Tech Tales Pro Reed: Bridging the Gap Between Technology and Creativity

Welcome to the world of Tech Tales Pro Reed, where innovation meets imagination! In an age defined by rapid technological advancements, creativity can sometimes take a backseat. But what if we told you that there’s a way to fuse both worlds seamlessly? Tech Tales Pro Reed is leading the charge in this exciting journey, guiding creators and tech enthusiasts alike toward new horizons. Whether you’re a budding artist or a seasoned developer, understanding how to balance technology with creativity opens up endless possibilities. Let’s delve into what makes Tech Tales Pro Reed such an essential player in this dynamic landscape.
What is Tech Tales Pro Reed?
Tech Tales Pro Reed is an innovative platform designed to merge the worlds of technology and creativity. It provides a space where tech enthusiasts and creative minds can intersect, share ideas, and collaborate on projects.
At its core, Tech Tales Pro Reed emphasizes storytelling through technology. Users can explore various tools that enhance their creative processes while leveraging technological advancements. This unique blend encourages experimentation and pushes boundaries in both fields.
The platform also offers resources such as tutorials, workshops, and case studies. These materials help individuals understand how to utilize technology effectively in their artistic endeavors. With a community-driven approach, Tech Tales Pro Reed fosters connections among creators from different backgrounds.
By encouraging dialogue between tech-savvy innovators and imaginative thinkers, it opens doors for new possibilities. Those who engage with Tech Tales Pro Reed discover not just solutions but inspiration for their next big project or idea.
The Importance of Balancing Technology and Creativity
Balancing technology and creativity is essential in today’s fast-paced world. Technology offers tools that can enhance artistic expression, but it shouldn’t overshadow the creative process itself.
When technology dominates, it may stifle innovative thinking. This imbalance can lead to a rigid approach where ideas become formulaic rather than inspired. Creativity thrives on exploration and spontaneity.
On the flip side, embracing technological advancements allows artists to push boundaries. Digital platforms open up new avenues for storytelling and design that were previously unimaginable.
The key lies in blending both worlds seamlessly. Finding harmony between tech innovations and personal expression leads to groundbreaking work that resonates with audiences on deeper levels.
This synergy fosters an environment where imagination flourishes alongside cutting-edge solutions, creating a rich tapestry of possibilities waiting to be explored.
How Tech Tales Pro Reed is Bridging the Gap
Tech Tales Pro Reed is redefining the intersection of technology and creativity. It provides a platform where innovators can share their stories, insights, and experiences.
Through workshops and collaborative projects, Tech Tales Pro Reed encourages creative minds to explore technological tools. This hands-on approach fosters an environment where ideas flourish.
The initiative also highlights successful collaborations between tech experts and artists. By showcasing these partnerships, it inspires others to think outside traditional boundaries.
Furthermore, the community aspect of Tech Tales Pro Reed enhances knowledge sharing among diverse individuals. Everyone brings unique perspectives that enrich discussions.
By integrating cutting-edge technologies into creative processes, this platform empowers creators to push limits. Thus, it nurtures a new generation of storytellers who blend artistry with innovation seamlessly.
Success Stories of Tech Tales Pro Reed
Tech Tales Pro Reed has ignited countless success stories across various fields. Creative minds have transformed their ideas into reality using its innovative tools.
One standout example comes from a small animation studio that struggled with traditional methods. After integrating Tech Tales Pro Reed, they streamlined production and enhanced collaboration among team members. The result? A captivating short film that gained international recognition.
Another inspiring tale involves an independent game developer who faced obstacles in bringing their vision to life. By leveraging the intuitive resources of Tech Tales Pro Reed, they crafted an immersive experience that captivated gamers worldwide, leading to record sales on launch day.
These stories show how blending technology and creativity can unlock untapped potential. Each journey is unique but shares a common thread: the powerful impact of Tech Tales Pro Reed in helping individuals realize their creative aspirations.
Tips for Incorporating Technology into Creative Projects
Embrace digital tools that enhance your creativity. Software like Adobe Creative Cloud offers endless possibilities for design and multimedia projects. Experiment with different applications to find what resonates with your style.
Use online platforms to collaborate. Websites such as Behance or Dribbble allow you to share work, gather feedback, and connect with other creatives. Community interaction can spark fresh ideas.
Incorporate social media strategically. Platforms like Instagram or TikTok are not just for sharing—they’re great for inspiration too. Follow thought leaders in your field and engage with their content.
Explore automation tools to streamline repetitive tasks in your creative process. Apps like Zapier can help manage workflows efficiently, giving you more time to focus on the artistic aspects of your projects.
Stay curious about emerging technologies such as virtual reality or artificial intelligence. They have the potential to unlock new dimensions in art and storytelling that could redefine creativity itself.
The Future of Technology and Creativity
The future of technology and creativity is poised for a dynamic transformation. As artificial intelligence and machine learning evolve, they will unlock new avenues for artistic expression. Imagine artists collaborating with AI to create breathtaking visuals or musicians using algorithms to compose unique soundscapes.
Virtual reality and augmented reality are also set to redefine how we experience art. These technologies can immerse audiences in interactive environments, allowing them to engage with creative works on an entirely different level.
Moreover, the rise of blockchain technology promises transparency in ownership and authenticity within the art world. This shift could empower creators by ensuring they receive fair compensation for their work.
As boundaries blur between disciplines, innovation will thrive. The fusion of tech-savvy creatives and traditional artists will lead to groundbreaking projects that challenge our perceptions and inspire future generations. The landscape ahead appears bright—and full of potential surprises waiting to unfold.
Conclusion
Tech Tales Pro Reed is more than just a concept; it’s a movement. By seamlessly merging technology with creativity, it opens new doors for innovation and artistic expression. The success stories that have emerged showcase the incredible potential when these two worlds collide.
As we look to the future, the synergy between technology and creativity only promises to grow stronger. Embracing this partnership will shape industries, inspire individuals, and drive societal change. Whether you’re an artist seeking new tools or a tech enthusiast wanting to explore your creative side, Tech Tales Pro Reed invites all of us to join in on this exciting journey.
The horizon is bright for those willing to bridge these realms together, ensuring that imagination knows no bounds as we navigate through our rapidly evolving digital landscape.
Technology
How the OIG’s First Compliance Guidance in 27 Years Rewrites the Rules for Retrospective Programs

27 Years of Silence, Then This
On February 3, 2026, the OIG published its Medicare Advantage Industry-wide Compliance Program Guidance, the first update to MA compliance guidance since 1999. For 27 years, the MA industry operated without updated federal compliance direction even as enrollment grew from under 10 million to over 33 million beneficiaries, risk adjustment payments expanded to over $615 billion annually, and coding practices evolved in ways the original guidance never anticipated.
The 2026 ICPG isn’t a suggestion. It’s the OIG’s formal articulation of enforcement priorities based on decades of audits, investigations, and enforcement actions. It identifies specific high-risk practices, names the compliance structures it expects organizations to maintain, and signals where enforcement attention will concentrate. For retrospective risk adjustment programs, the guidance is specific and direct.
What the Guidance Says About Chart Reviews
The ICPG flags three retrospective practices as suspect for inflating risk scores: chart reviews that only add diagnoses without removing unsupported ones, in-home health risk assessments that generate diagnoses never considered in patient care, and EHR prompts designed to surface diagnosis codes for risk adjustment purposes rather than clinical decision-making.
On chart reviews specifically, the guidance warns that failing to remove unsupported codes is a compliance failure, not just an operational gap. This is significant because it frames deletion as an obligation, not an option. Plans that run add-only programs aren’t just missing an opportunity to clean their data. They’re failing to meet a compliance expectation the OIG has now formally published.
The guidance recommends that plans audit high-risk diagnosis codes both before and after CMS submission. That’s a two-phase validation process: pre-submission review to catch problems before they’re submitted, and post-submission surveillance to catch problems that develop after submission as documentation ages or conditions change.
What the Guidance Means for Program Design
The ICPG effectively creates a compliance blueprint for retrospective programs. Plans can evaluate their own operations against what the OIG explicitly identified as expected practices and high-risk activities. The gap analysis is straightforward: does your program only add codes? That’s flagged. Does your program remove unsupported codes? That’s expected. Do you audit high-risk diagnoses before and after submission? That’s recommended.
Plans that aligned their programs to these standards before the guidance was published are in strong compliance positions. Plans that didn’t now have a documented standard they’re measurably failing to meet. The guidance doesn’t create new law, but it creates the framework OIG will use to evaluate compliance during investigations, audits, and enforcement actions.
The timing matters. The guidance arrived alongside $670+ million in DOJ settlements, OIG audits with 80-91% error rates, and congressional investigations. It’s not an isolated document. It’s the compliance framework that contextualizes everything else the government has done in risk adjustment enforcement over the past two years.
The Retrospective Program Checklist
Every Retrospective Risk Adjustment program should be evaluated against the ICPG’s explicit standards: two-way coding that adds and removes, pre-submission MEAT validation, post-submission surveillance, audit of high-risk diagnosis categories, and evidence trails that document every coding decision. Plans that meet these standards are aligned with the OIG’s published expectations. Plans that fall short now have a public document that quantifies exactly how far short they fall, and that document will be referenced in every future enforcement action.
Technology
0800 033 8055: Who Is Calling and What You Should Know

In today’s digital world, unknown phone calls have become a common part of everyday life. One number that many people are searching for is 0800 033 8055. If you’ve recently received a call from this number, you’re probably wondering whether it’s safe, legitimate, or something you should avoid. Understanding who is behind such calls can help you make smarter decisions and protect yourself from potential scams.
This article explores everything you need to know about 0800 033 8055, including possible sources of the call, why you might be contacted, and what steps you should take if you receive a call from this number.
Understanding the Nature of 0800 Numbers
Before diving into the specifics of 0800 033 8055, it’s important to understand what 0800 numbers actually are. These numbers are typically known as “freephone” numbers, meaning that the person receiving the call does not pay for it. Instead, the organization or business calling you covers the cost.
Because of this setup, 0800 numbers are commonly used by customer service departments, marketing teams, and support centers. Companies use them to reach customers without charging them for the call. However, not every 0800 number is automatically trustworthy, as scammers have also found ways to use similar formats.
The presence of an 0800 prefix doesn’t guarantee legitimacy. It simply indicates the type of number being used. This is why it’s important to investigate further when you encounter a number like 0800 033 8055, especially if the call seems unexpected or suspicious.
Why You Might Receive a Call from 0800 033 8055
There are several reasons why 0800 033 8055 might appear on your phone. In many cases, such numbers are used by companies for outbound communication. This could include customer support follow-ups, service updates, or promotional offers.
Sometimes, financial institutions, telecom providers, or insurance companies use 0800 numbers to reach their customers. If you have recently interacted with a service provider, signed up for a product, or requested information, the call could be related to that activity.
On the other hand, unsolicited calls can also come from telemarketing campaigns. These calls may try to offer deals, surveys, or services that you didn’t request. In such situations, it’s important to stay cautious and avoid sharing personal information unless you are certain about the caller’s identity.
Is 0800 033 8055 Legitimate or a Scam?
One of the most common concerns people have about 0800 033 8055 is whether it is legitimate. The truth is that the legitimacy of a number depends on how it is being used rather than the number itself.
In some cases, users report that calls from this number are linked to genuine organizations. These could include service providers or companies conducting customer outreach. However, there are also instances where people feel the calls are intrusive or suspicious, especially when the caller asks for personal details.
Scammers sometimes spoof or imitate real numbers to gain trust. This means that even if a number looks official, it could still be used for fraudulent purposes. That’s why it’s essential to verify the caller’s identity before taking any action or sharing sensitive information.
Common Complaints About 0800 033 8055
Many individuals who search for 0800 033 8055 do so because they’ve experienced repeated or unexpected calls. One common complaint is the frequency of calls, with some users reporting multiple attempts within a short period.
Another issue people mention is the lack of clarity about who is calling. In some cases, the caller may not clearly identify themselves or the company they represent. This can make the call feel suspicious and uncomfortable.
Some users also report that the calls are automated or involve scripted conversations. These types of calls are often associated with telemarketing or data collection efforts, which can be frustrating if you did not consent to being contacted.
How to Handle Calls from 0800 033 8055
If you receive a call from 0800 033 8055, the best approach is to remain calm and cautious. Answering the call is not necessarily harmful, but you should avoid sharing any personal or financial information unless you are completely sure about the caller’s identity.
If the caller claims to represent a company, you can ask for their name, department, and reason for calling. A legitimate caller should be able to provide clear and verifiable information. If anything feels off, it’s perfectly okay to end the call.
You can also choose to ignore the call and let it go to voicemail. If it’s important, the caller will usually leave a message explaining the purpose of the call. This gives you time to assess whether you want to respond or not.
Should You Call Back 0800 033 8055?
Many people wonder whether they should return a missed call from 0800 033 8055. While 0800 numbers are generally free to call, it’s still important to be cautious when calling back unknown numbers.
If the call was legitimate, the caller will likely try again or leave a message with instructions. Calling back without knowing who you’re contacting could lead to unnecessary interactions or even potential risks.
A safer approach is to verify the number through trusted sources or contact the company directly using official contact details. This ensures that you are communicating with the right organization and not a potential scammer.
How to Protect Yourself from Unwanted Calls
Dealing with numbers like 0800 033 8055 highlights the importance of protecting yourself from unwanted or suspicious calls. One effective method is to use call-blocking features available on most smartphones.
You can also register your number with services that limit unsolicited marketing calls. While this may not stop all calls, it can significantly reduce the number of unwanted contacts you receive.
Staying informed is another key step. By researching numbers and understanding common scam tactics, you can make better decisions and avoid falling victim to fraudulent schemes.
When to Report a Suspicious Call
If you believe that a call from 0800 033 8055 is suspicious or potentially fraudulent, it’s a good idea to report it. Reporting helps authorities track and address scam activities, protecting others from similar experiences.
You can report such calls to your telecom provider or relevant consumer protection agencies. Providing details about the call, such as the time, content, and behavior of the caller, can be very helpful.
Taking action not only protects you but also contributes to a safer communication environment for everyone. Even if the call turns out to be harmless, reporting concerns can still be beneficial.
The Growing Issue of Unknown Callers
The rise of numbers like 0800 033 8055 reflects a broader trend in modern communication. As businesses and scammers alike use phone calls to reach people, it has become increasingly difficult to distinguish between legitimate and unwanted contacts.
Technology has made it easier to connect with people, but it has also opened the door to misuse. This is why awareness and caution are more important than ever when dealing with unknown numbers.
By staying informed and following best practices, you can navigate this landscape with confidence. Whether the call is genuine or not, your safety and privacy should always come first.
Final Thoughts on 0800 033 8055
In conclusion, 0800 033 8055 is a number that has caught the attention of many people due to unexpected or repeated calls. While it may be associated with legitimate businesses in some cases, it’s important to approach such calls with caution.
Understanding the nature of 0800 numbers, verifying the identity of callers, and protecting your personal information are essential steps in handling these situations. Not every call is harmful, but staying alert ensures that you avoid potential risks.
If you receive a call from 0800 033 8055, take your time to assess the situation and decide how to respond. By being informed and cautious, you can manage unknown calls effectively and maintain control over your communication.
-

 Technology4 months ago
Technology4 months agoLibnk: Revolutionizing Collaboration in the Digital Age
-

 Lifestyle4 months ago
Lifestyle4 months agoPyjamaspapper: The Perfect Blend of Style and Comfort for Night Sleep
-

 Technology3 months ago
Technology3 months agoWhat is Voozon.com? Is This the Best Website for Your Needs?
-

 Blog3 months ago
Blog3 months agoFlagbeez Com: Affordable and Stylish Flags for Every Occasion
-

 Technology4 months ago
Technology4 months agoThe Future of Fapell: Innovations and Possibilities Ahead
-

 Technology4 months ago
Technology4 months agoUpTheSwitchLLC: Revolutionizing Your Energy Solutions
-

 Entertainment4 months ago
Entertainment4 months agoLwedninja: Revolutionizing Online Content Creation
-
 Lifestyle4 months ago
Lifestyle4 months agoHaskawana: How to Enjoy While Preserving Its Beauty
